Identity-First
Architecture
Built from the ground up for identity governance, not bolted on to code scanners and ASPM tools
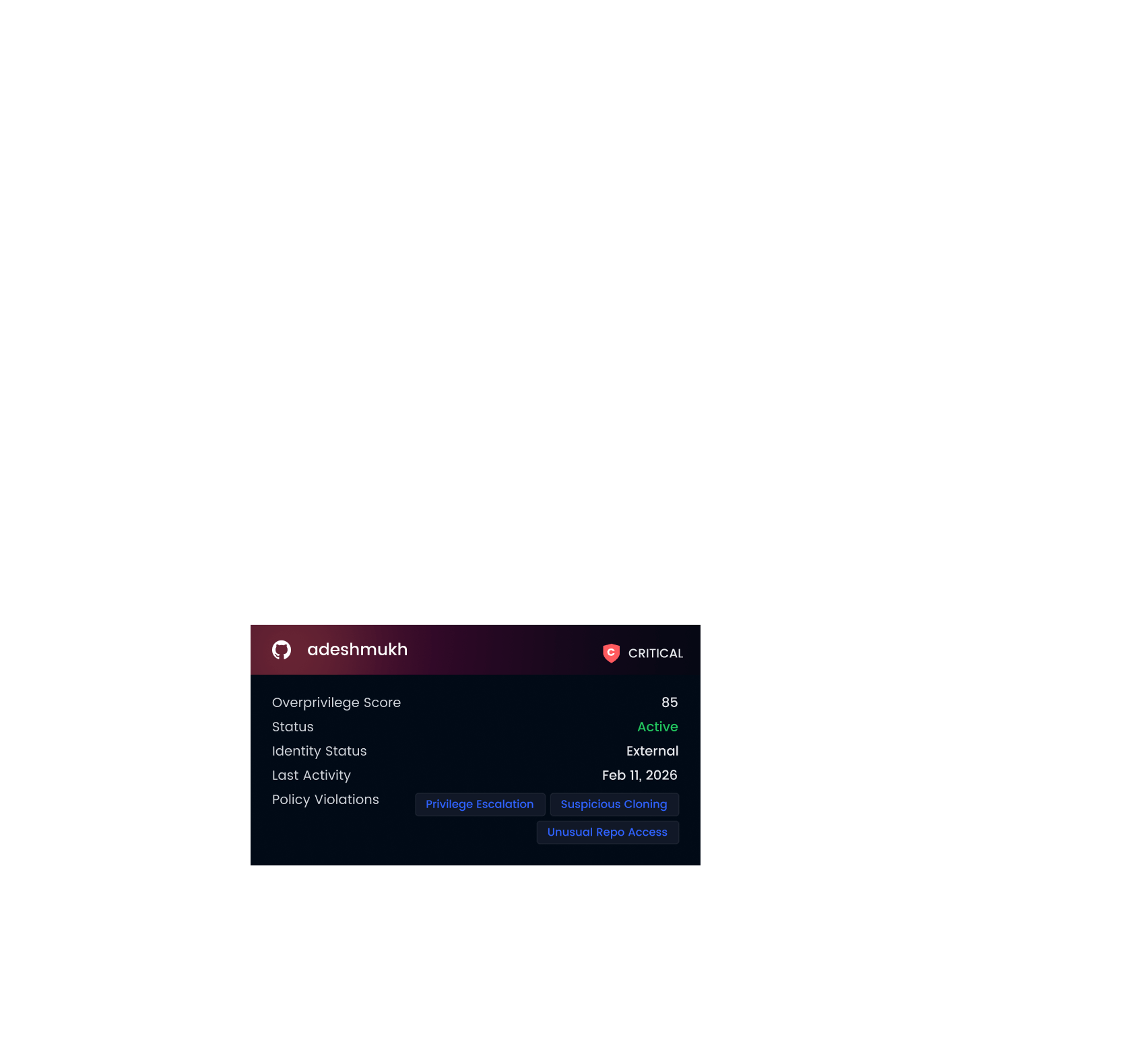
Complete visibility into every human, non-human, and AI identity across your SDLC
Automatically correlates identities across all your tools
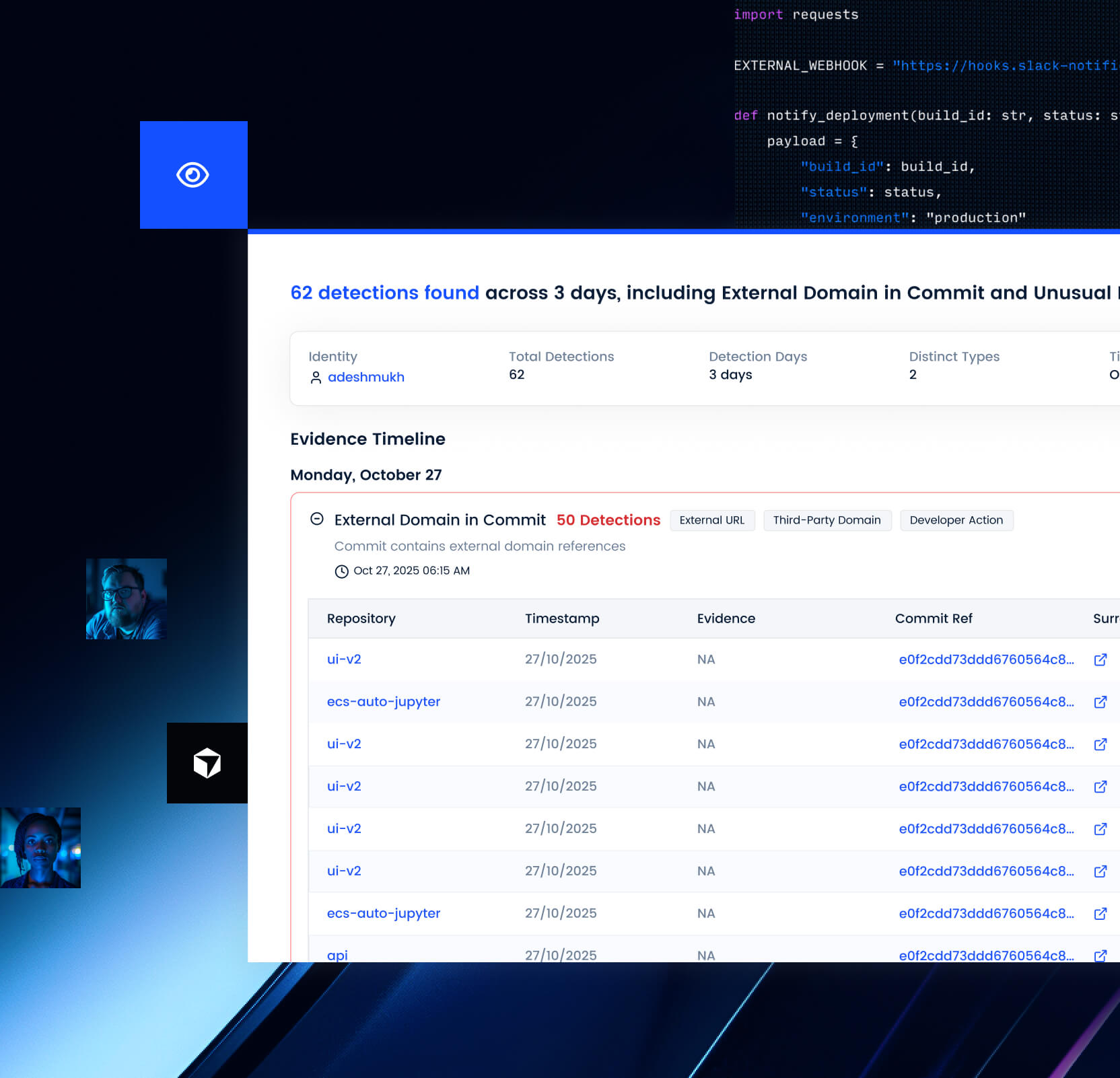
See WHO did WHAT and WHY it's a risk